OpenClaw Founder Issues Warning: CLAW Fake Airdrop Scams Incoming, GitHub Developers Targeted

OpenClaw founder Peter Steinberger issued a public warning on the X platform on March 19, urging all users to treat any emails claiming to be related to OpenClaw cryptocurrency as scams. He explicitly stated that OpenClaw is an “open-source and non-commercial” project. Previously, multiple developers had reported a large-scale phishing attack targeting GitHub users worldwide.
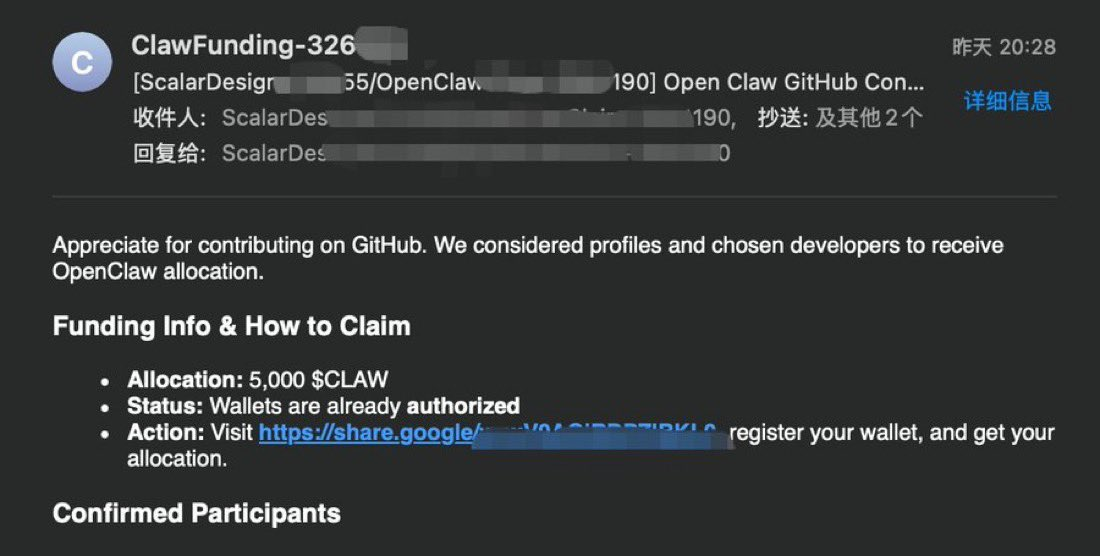
Details of the Phishing Attack: Impersonating GitHub Notifications Sweeping Developers
(Source: X)
The attack was carefully designed to be difficult to identify immediately. Security researcher Aoke Quant suspects that the attacker directly scraped developers’ publicly available contact information from GitHub to facilitate large-scale targeted dissemination.
The main features of the phishing emails include:
Sender Spoofing: The emails mimic the official GitHub notification format, making them hard to distinguish from legitimate messages.
Fake Sender Accounts: Accounts such as “ClawFunding” and “ClawReward” were used to impersonate legitimate entities.
Content Deception: The emails claim that the recipient has been listed as a “Featured Contributor,” creating a sense of exclusivity and urgency.
Call to Action: Users are guided to click suspicious Google links to “claim” fake tokens.
Multilingual Versions: Some emails have been translated into Spanish, indicating the attack has spread across multiple regions.
Developer Daniel Sánchez, sharing screenshots of the reports, pointed out: “Offering free funds proactively is almost certainly a scam. Open-source projects have no reason to conduct any kind of cryptocurrency giveaways.”
Complete Timeline of Months-Long Harassment: From Meme Coins to Account Hacks in 30 Seconds
This wave of phishing attacks is the latest escalation in months of systematic harassment against OpenClaw. Since OpenClaw gained popularity in January this year under the name “Clawdbot,” cryptocurrency speculators have launched ongoing multi-layered attacks against Steinberger and his project.
Key events include:
Meme Coin Creation: Scammers unauthorizedly issued a meme coin named after OpenClaw on Solana, which plummeted 96% in one day, causing significant losses for retail investors.
Brand Rebranding Crisis: Due to trademark issues, Anthropic demanded Steinberger rename the robot. After he changed “Clawdbot” to “Moltbot,” attackers invaded the original account in less than five seconds, promoting new scam tokens and spreading malware before Steinberger could secure the account.
GitHub Account Compromise: His GitHub username was hacked in about 30 seconds, used to distribute malicious code.
Discord Ban: Facing continuous spam of token hashes, Steinberger was forced to ban all cryptocurrency-related discussions on his Discord server.
X Notifications Disabled: Continuous spam of token hashes and junk messages made X (Twitter) notifications unusable.
Steinberger described this entire experience as the “most severe online harassment” he has faced. Even after joining OpenAI in February 2026, leading the personal AI agent division under Sam Altman, and with backing from a major tech company, scammers continued to exploit the OpenClaw brand for profit.
Frequently Asked Questions
Q: How can I identify fake OpenClaw phishing emails?
According to Steinberger’s public warning, the most effective methods are: First, OpenClaw does not have any official cryptocurrency tokens (no “CLAW” or any other tokens). Second, any email requesting you to click links to “claim airdrops” or “connect your wallet” is a scam. Third, only trust OpenClaw’s official website as the sole source of verified information, and remain cautious of third-party commercial packaging. Security experts recommend verifying the sender’s domain carefully, even if the email appears to come from an official GitHub address, as scammers often spoof display names.
Q: Does OpenClaw’s security vulnerability facilitate phishing attacks?
Security firm SlowMist previously warned that improperly configured Clawdbot/OpenClaw instances could leak API keys and private chat logs. Researcher Jamieson O’Reilly also found that unauthenticated instances might expose hundreds of credentials. These vulnerabilities could allow scammers to access real user data, enabling them to craft highly convincing phishing emails and increase scam success rates. All users deploying OpenClaw are advised to ensure proper authentication setup and regularly rotate API keys.
Q: How should I respond to similar phishing attacks?
If you receive any emails claiming to be related to OpenClaw cryptocurrency airdrops, delete and mark them as phishing immediately. Do not click any links or provide personal information. If you have clicked a link, change all related account passwords, revoke suspicious third-party permissions, and scan your device for malware. Report the phishing activity through official OpenClaw channels to help protect other developers in the community.