Ethereum Foundation Establishes "Post-Quantum Safety Team," Targets 2029 for Protocol-Layer Upgrade

Members of the Ethereum Foundation officially launched the “Post-Quantum Ethereum” resource center this Tuesday, announcing the formation of a dedicated post-quantum security team. The plan is to implement quantum-safe solutions at the protocol layer by 2029, followed by advancing upgrades at the execution layer. The team pointed out that quantum computing currently does not pose an immediate threat to cryptocurrencies, but given the complexity of the upgrade process involving multiple coordinated efforts, early preparation is necessary.
Why Quantum Computing Is a Long-Term Security Issue for Ethereum
Once quantum computers reach sufficient computational power, existing elliptic curve cryptography (ECC) could theoretically be broken, directly threatening private key security and wallet protection mechanisms. Galaxy Digital analyst Will Owens noted that the primary risk is concentrated on wallets with exposed public keys; meanwhile, Charles Edwards of Capriole Investments believes that, in the long run, all crypto assets face quantum threats.
The post-quantum team emphasizes that the real challenge of the upgrade is not algorithm selection but the complexity of implementation itself: “Migrating a decentralized global protocol requires years of coordination, engineering design, and formal verification. This work must begin before the threat becomes imminent.” Ethereum currently safeguards billions of dollars in assets, and any delay in upgrades could create a significant security exposure window once quantum technology matures.
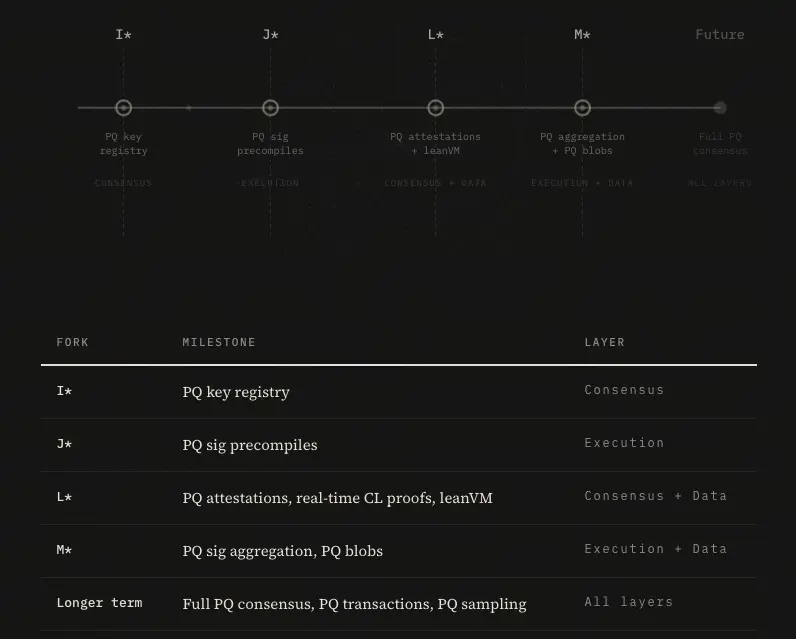
SNARK Architecture and Three-Phase Upgrade Roadmap
(Source: Ethereum Post-Quantum Security Team)
The post-quantum team plans to integrate SNARK (Succinct Non-Interactive Argument of Knowledge) technology as the core approach for quantum-safe signatures, addressing issues where some quantum-secure signature schemes require large computational resources, leading to increased bandwidth and storage demands that impact network performance. The upgrade will cover three core technical layers of Ethereum:
Consensus Layer: Post-quantum modifications to validator signatures and block confirmation mechanisms
Execution Layer: Quantum-safe upgrades to smart contract execution environments and transaction signatures, to be implemented after protocol layer deployment
Data Layer: Reinforcement measures related to data availability and storage security
In terms of asset protection priority, standard Ethereum wallets are the primary target due to their concentration of the largest value holdings, followed by high-value operational wallets associated with cryptocurrency exchanges, cross-chain bridges, and custody solutions.
Major Challenge: How to Complete Upgrades Without Network Disruption
The post-quantum team states that algorithm selection is just the starting point. More complex issues include securely upgrading hundreds of millions of existing accounts, ensuring the migration process does not introduce new vulnerabilities, avoiding creating new attack surfaces, maintaining current performance levels, and coordinating ecosystem-wide adoption. This series of engineering and coordination challenges forms the core rationale for “initiating now and completing the first phase by 2029.”
Frequently Asked Questions
Q: How significant is the current threat of quantum computers to Ethereum?
The post-quantum Ethereum team clearly states that there is no imminent quantum threat at present. Current quantum computers lack the computational power to break the cryptographic mechanisms used by Ethereum. However, due to the long-term complexity of the upgrade process, early deployment is considered a necessary preventative measure.
Q: Why does the post-quantum upgrade take several years to complete?
Ethereum is a decentralized global protocol. Security upgrades require cross-layer coordination across consensus, execution, and data layers, involving the migration of hundreds of millions of accounts and the adoption of changes across the global ecosystem. Each step requires rigorous formal verification to ensure the upgrade process itself does not introduce new security vulnerabilities.
Q: How does SNARK address the performance issues of quantum-safe signatures?
Some quantum-safe signature schemes are computationally more complex than current mechanisms, potentially significantly increasing network bandwidth and storage requirements. SNARKs use zero-knowledge proofs to compress computational overhead, enabling quantum-safe protection while minimizing performance impact.